The CVE-2026-41940 cpanel Exploit
Table of Contents
▼▼▼▼▼
What Happened?
Was It Serious?
How DId It Happen?
Who Did It Effect?
How We Handled it
What You Should Do?
Going Forward
Final Thoughts
Need Hosting?
Join Orange Website today and host your site on infrastructure designed for stability, performance, and peace of mind.
What Happened With the Recent cPanel Security Vulnerability?
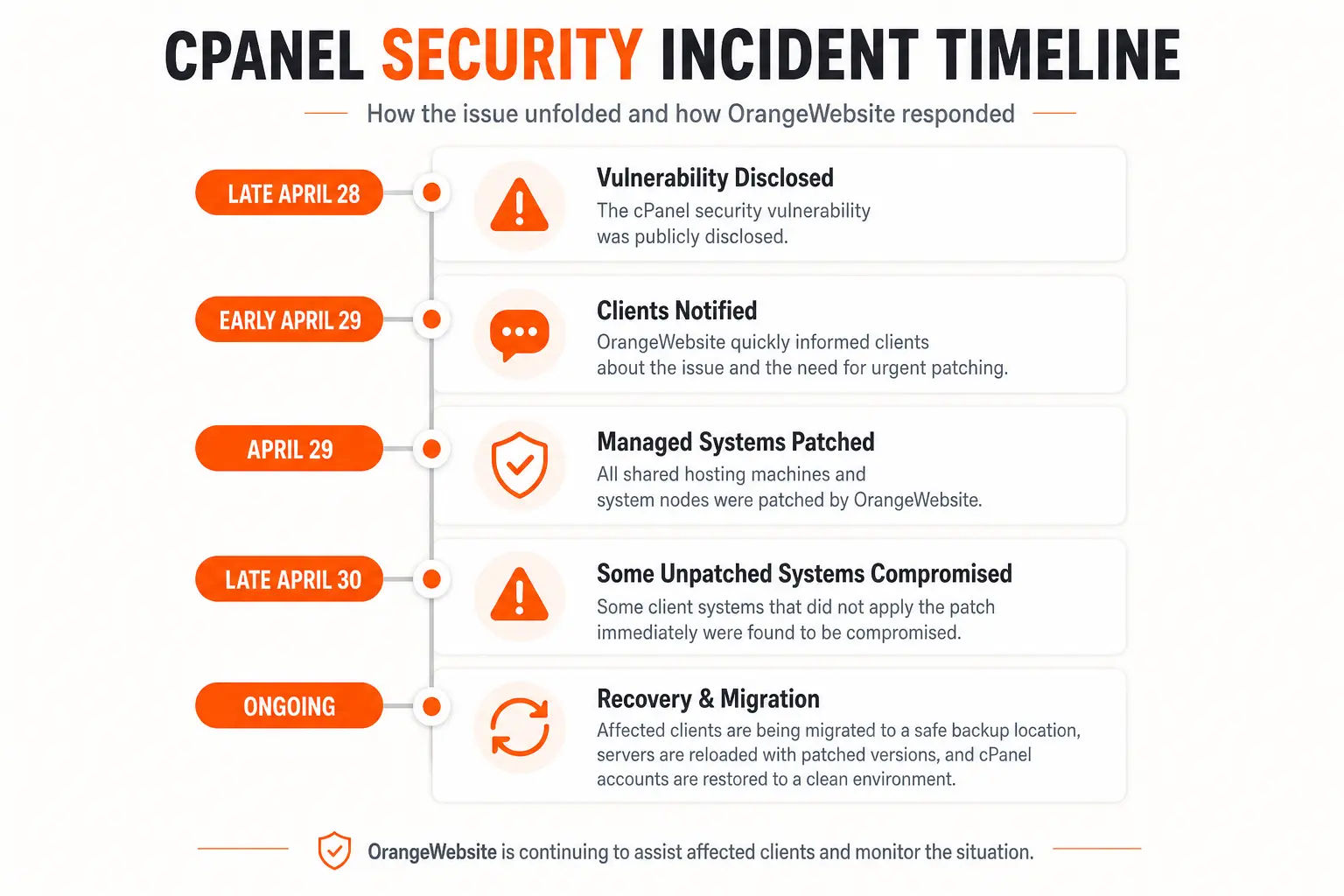
On April 28, 2026, cPanel released an important security update for cPanel & WHM and WP Squared after a serious vulnerability was discovered in the software. The vulnerability is now tracked as CVE-2026-41940 and has been widely reported as a critical authentication bypass issue affecting cPanel & WHM installations. cPanel confirmed that the issue affected cPanel software, including DNSOnly, on versions after 11.40.
Because cPanel and WHM are used across a large part of the web hosting industry, this quickly became a major concern for hosting providers, server administrators, and website owners. TechCrunch reported that attackers were actively exploiting the bug and that the issue could allow hackers to bypass the normal login process and gain access to the administration panel of affected systems.
At OrangeWebsite, we treated this as a high-priority security event from the moment it was disclosed. The vulnerability was disclosed late on April 28, and we announced it to our clients early on April 29. We also patched all shared hosting machines and system nodes as quickly as possible to protect customers on OrangeWebsite-managed infrastructure.
What Was the cPanel Vulnerability?
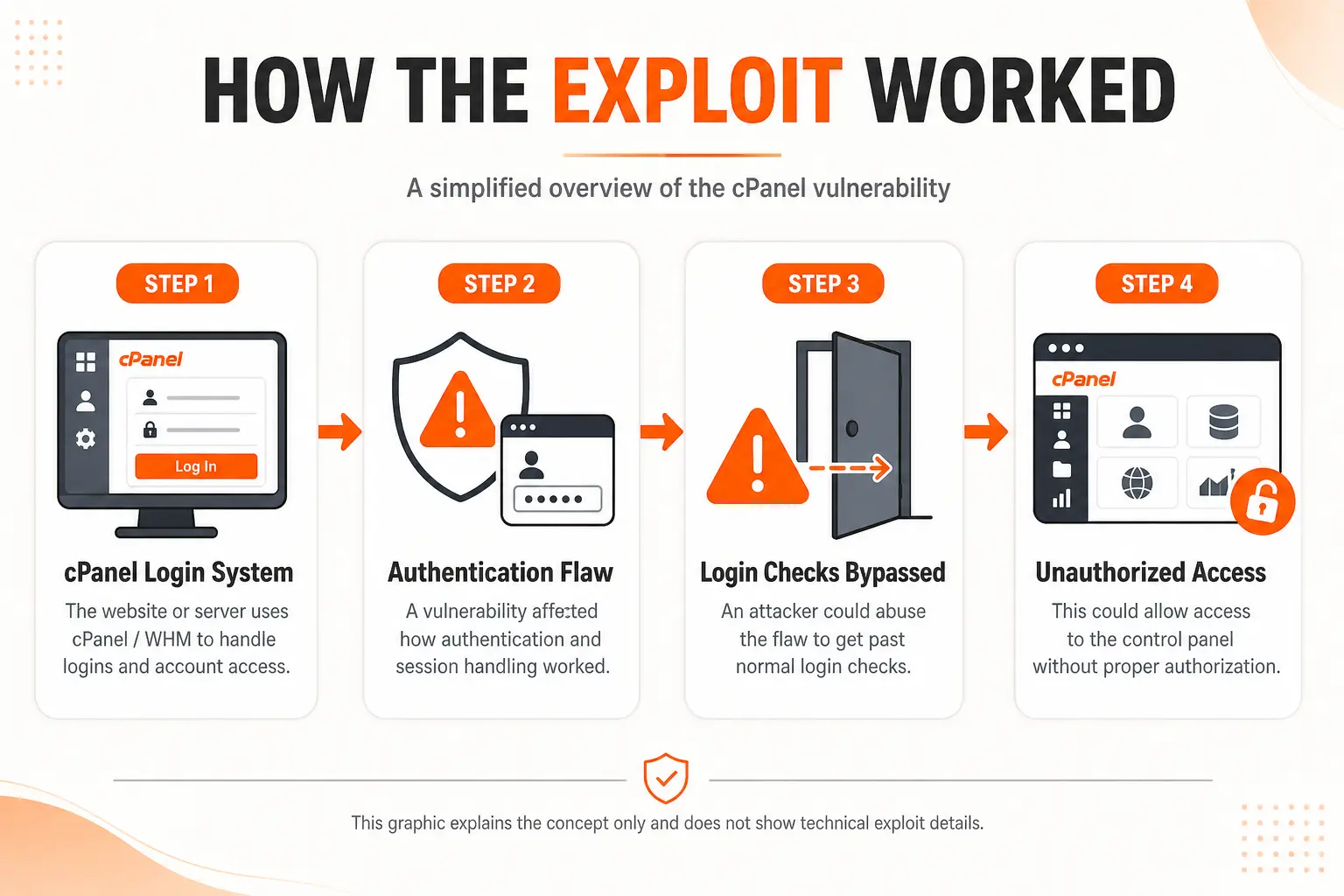
In simple terms, this vulnerability affected the login process of cPanel & WHM.
Normally, to access cPanel or WHM, a user needs valid login details. That means a username, password, and in many cases, additional security checks such as two-factor authentication. This vulnerability created a way for attackers to bypass that normal authentication process under certain conditions.
That is why this type of vulnerability is called an authentication bypass.
An authentication bypass is dangerous because it does not work like a normal password attack. The attacker does not necessarily need to know your password, guess your password, or trick you into giving it away. Instead, the attacker takes advantage of a flaw in how the software handles the login or session process.
Security researchers described CVE-2026-41940 as a critical issue because successful exploitation could allow an unauthenticated remote attacker to gain unauthorized administrative access to affected cPanel & WHM systems. Rapid7 noted that cPanel & WHM provides server-level administration, meaning a successful compromise could affect websites, databases, configurations, and accounts managed through that server.
Why Was This So Serious?
cPanel and WHM are not just simple website dashboards. They are powerful tools used to manage hosting accounts, websites, email accounts, files, DNS settings, databases, SSL certificates, and server-level configurations.
For a normal website owner, cPanel is often the place where they manage their website files, email accounts, redirects, backups, and databases.
For a server administrator or hosting company, WHM is even more powerful. WHM can manage multiple cPanel accounts on the same server. This means that if an attacker gains high-level access to WHM, the risk can extend beyond one single website.
That is why this vulnerability was treated as urgent across the hosting industry. TechCrunch reported that cPanel & WHM are widely used by hosting companies and website owners around the world, and that the affected software has deep access to the servers it manages.
In practical terms, a successful attack could potentially allow a hacker to interfere with hosted websites, access sensitive files, change configurations, create unauthorized access, or compromise customer accounts on an affected server.
How Did the Exploit Happen?
The technical details are complex, but the simple explanation is this:
The vulnerability was connected to how cPanel handled login sessions. A session is what tells the system, “this user has logged in successfully and is allowed to access this area.”
When you log into a website, control panel, or online account, the server usually creates a session for you. That session helps the system remember that you are already logged in, so you do not have to enter your password again on every single page.
In this case, the flaw allowed attackers to interfere with the session process in a way that could make the system treat them as authenticated when they should not have been.
Some technical writeups describe the issue as involving CRLF injection and session handling, but the important point for customers is simpler: attackers found a way to abuse the login/session system to get access without going through the normal login process. Rapid7 described the vulnerability as an authentication bypass caused by a CRLF injection in the login and session loading processes of cPanel & WHM.
This is also why patching was so important. The fix needed to happen at the software level. Changing a website password alone would not fix the underlying vulnerability if the server itself was still running an affected version of cPanel.
Who Was Affected?
According to cPanel’s advisory, the vulnerability affected cPanel software, including DNSOnly, on versions after 11.40. cPanel released patched versions across multiple supported cPanel & WHM versions and also released a patch for WP Squared.
The main risk applied to servers running affected versions of cPanel & WHM that had not yet been patched.
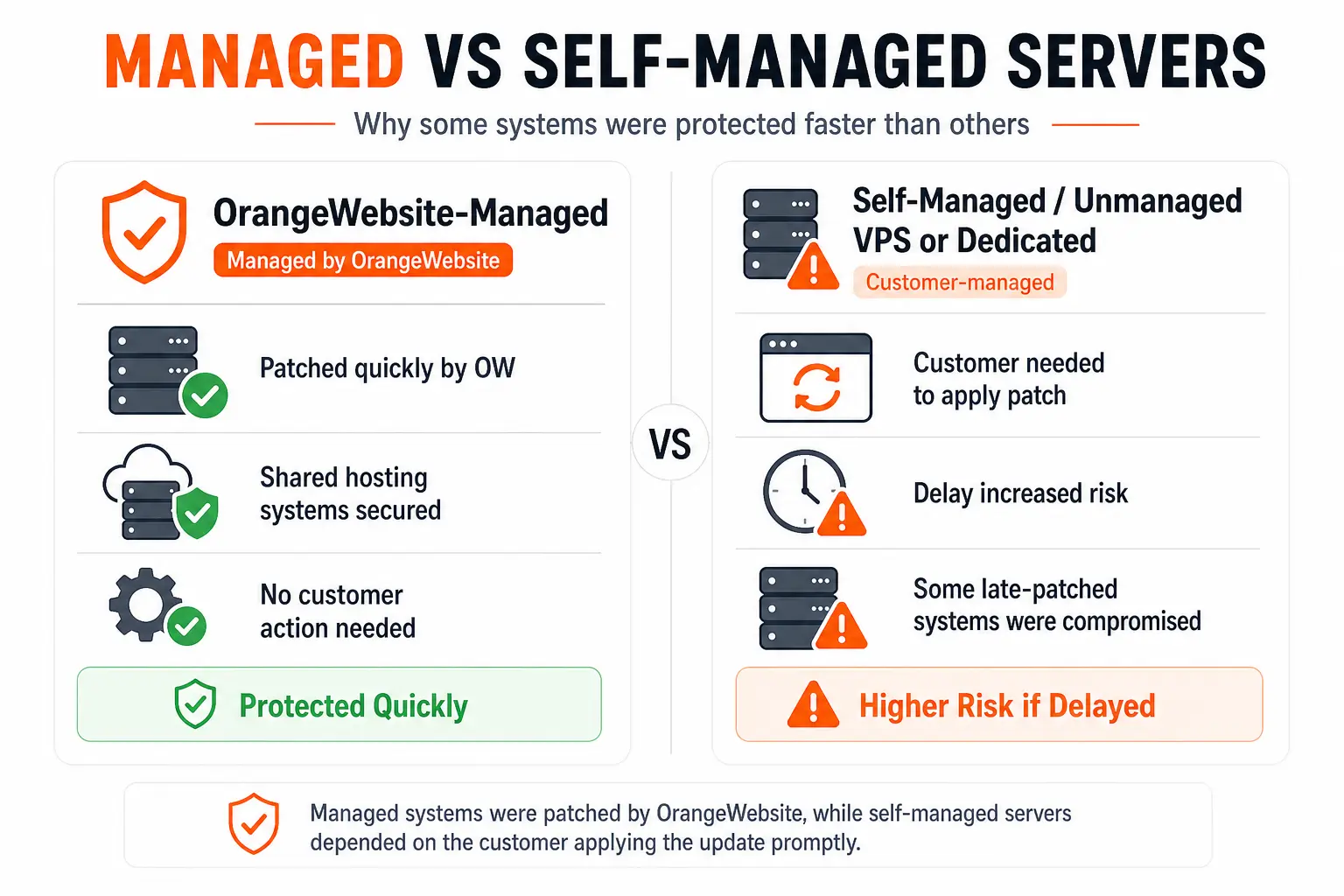
For OrangeWebsite shared hosting customers, we patched the shared hosting environment and system nodes quickly after the disclosure. Customers on fully managed OrangeWebsite infrastructure did not need to manually apply the cPanel update themselves.
However, some customers using their own VPS, dedicated server, or self-managed environment may have needed to apply the patch manually. Unfortunately, some clients who did not apply the patch immediately appear to have been affected by late April 30.
What Did OrangeWebsite Do?
Once the issue was disclosed late on April 28, OrangeWebsite began responding immediately.
Early on April 29, we announced the issue to our clients and started patching all OrangeWebsite-managed machines. This included shared hosting servers and system nodes.
Our priority was to secure our infrastructure as quickly as possible and reduce the risk for customers hosted on OrangeWebsite-managed systems.
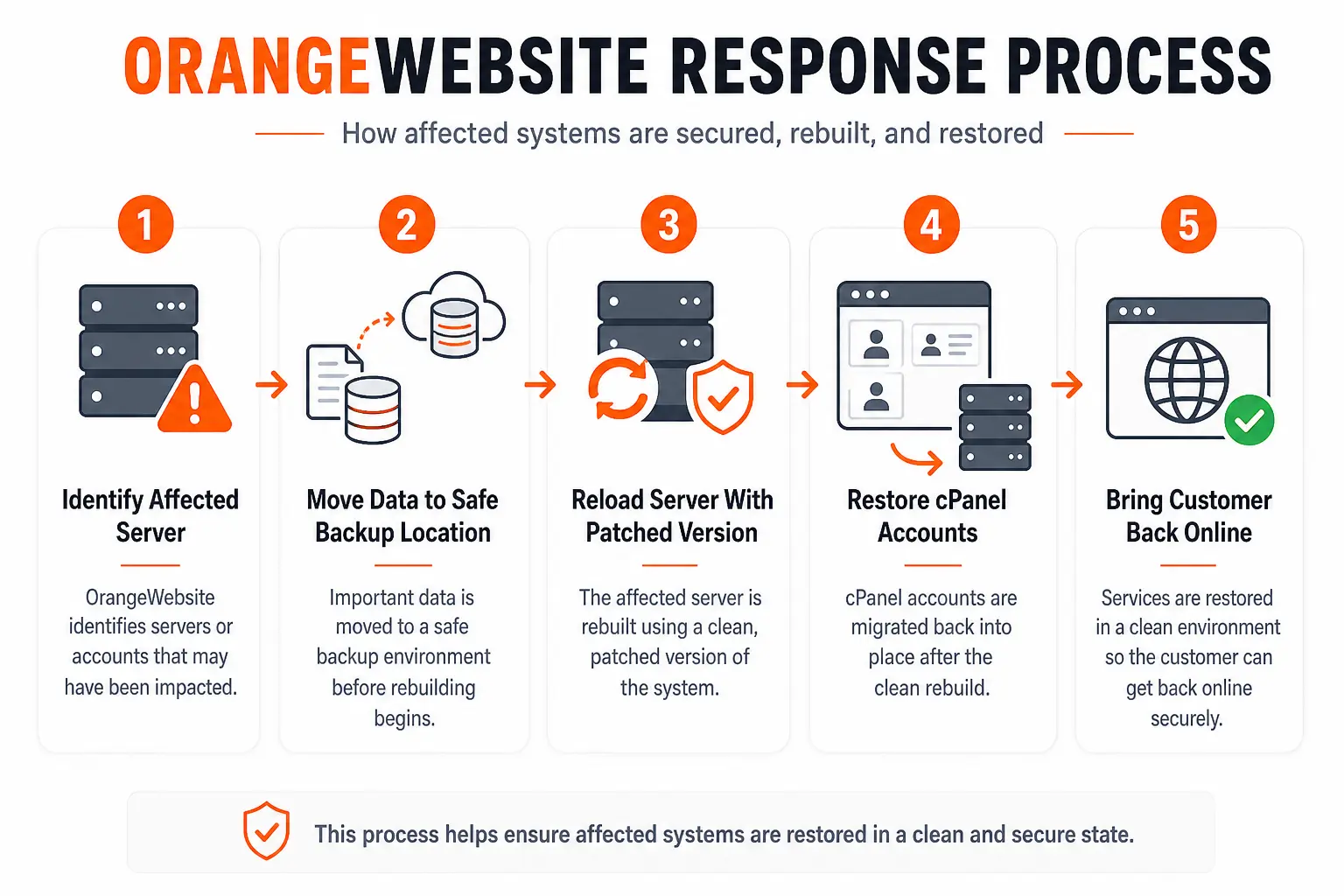
For affected customers, we are also taking additional recovery steps. In cases where a client server appears to have been compromised, we are working directly with the client to migrate their data to a safe backup location while the affected server is reloaded with a clean, patched version. Once the server has been rebuilt and secured, the customer’s cPanel accounts are migrated back into place.
This process is more careful than simply applying a patch after the fact. If a server has already been compromised, patching the vulnerability is only one part of the job. The safer approach is to assume the affected environment may no longer be trustworthy, preserve the customer’s data, rebuild the server cleanly, apply the patched version, and then restore the accounts from a clean source.
Why Not Just Patch Every Compromised Server and Leave It Online?
This is an important question.
Patching protects against future exploitation of the vulnerability, but it does not automatically remove anything an attacker may have already changed before the patch was applied.
If a server was compromised before being patched, there may be unknown changes on that server. An attacker could have added files, created access methods, changed configurations, or modified accounts. In that situation, simply applying the patch would close the original door, but it would not guarantee that the server was clean.
That is why OrangeWebsite is rebuilding affected servers instead of only patching them in place.
The goal is not just to fix the vulnerability. The goal is to return affected customers to a clean and secure environment.
What Should Customers Do?
If you are an OrangeWebsite shared hosting customer, OrangeWebsite has already patched the shared hosting machines and system nodes under our management.
If you manage your own cPanel server, VPS, or dedicated server, you should make sure your system has been updated to one of the patched cPanel versions. cPanel’s official advisory recommends running the cPanel update script, verifying the installed version, and restarting the cPanel service after the update.
Customers who manage their own servers should also check whether automatic cPanel updates were disabled or pinned to a specific version. cPanel warned that servers with disabled or pinned update settings may not automatically update and should be updated manually as a priority.
If you believe your server may have been compromised, the safest next steps are to contact support, avoid making unnecessary changes, preserve logs where possible, and allow the server to be reviewed properly. In some cases, a clean rebuild and migration may be the most responsible recovery option.
What Is OrangeWebsite Doing Going Forward?
Security events like this are exactly why fast patching, active monitoring, and proper server management matter.
OrangeWebsite will continue monitoring the situation, assisting affected clients, and rebuilding compromised environments where necessary. We are also continuing to follow official cPanel guidance as new updates and detection methods become available.
cPanel has updated its advisory multiple times since the original publication, including adding patched versions and updating detection guidance.
Our focus is simple: protect customer data, keep websites online where possible, and make sure any affected environment is restored in a clean and secure state.
Final Thoughts
The CVE-2026-41940 vulnerability was a serious issue because it affected the login and session handling process of one of the most widely used hosting control panels in the world.
For customers, the key thing to understand is that this was not a normal website hack, weak password issue, or WordPress plugin problem. It was a vulnerability in the server control panel software itself.
OrangeWebsite responded quickly by notifying clients, patching managed systems, and working directly with affected customers whose servers were not patched in time. Where compromise is suspected or confirmed, we are taking the safer route: moving customer data to a backup location, rebuilding the affected server with a patched version, and restoring accounts back into a clean environment.
Security issues can move fast, but so can responsible action. In this case, fast patching, transparent communication, and careful recovery are the most important steps toward keeping customers protected.