HAND CRAFTED GUIDES AND ARTICLES BY INDUSTRY EXPERTS
OrangeWebsite hosting articles are designed to guide your way around a rather complex and rapidly changing industry. On this website, you will find many helpful web hosting guides and tutorials. Helping you to find solutions for general and less common web hosting-related dilemmas.
Our writing team is a group of people with years of experience in the web hosting industry. If you have any questions or ideas about the material published on our website, please get in touch with us anytime. We update our website and add new articles every week.
Top 5 ARK PVE Servers
The 5 Best ARK PVE ServersWhen it comes to immersive and engaging gameplay, ARK has set a standard...
How to Improve Your SEO in 2024
How to Improve Your SEO in 2024If you've been involved in the internet for any substantial period,...
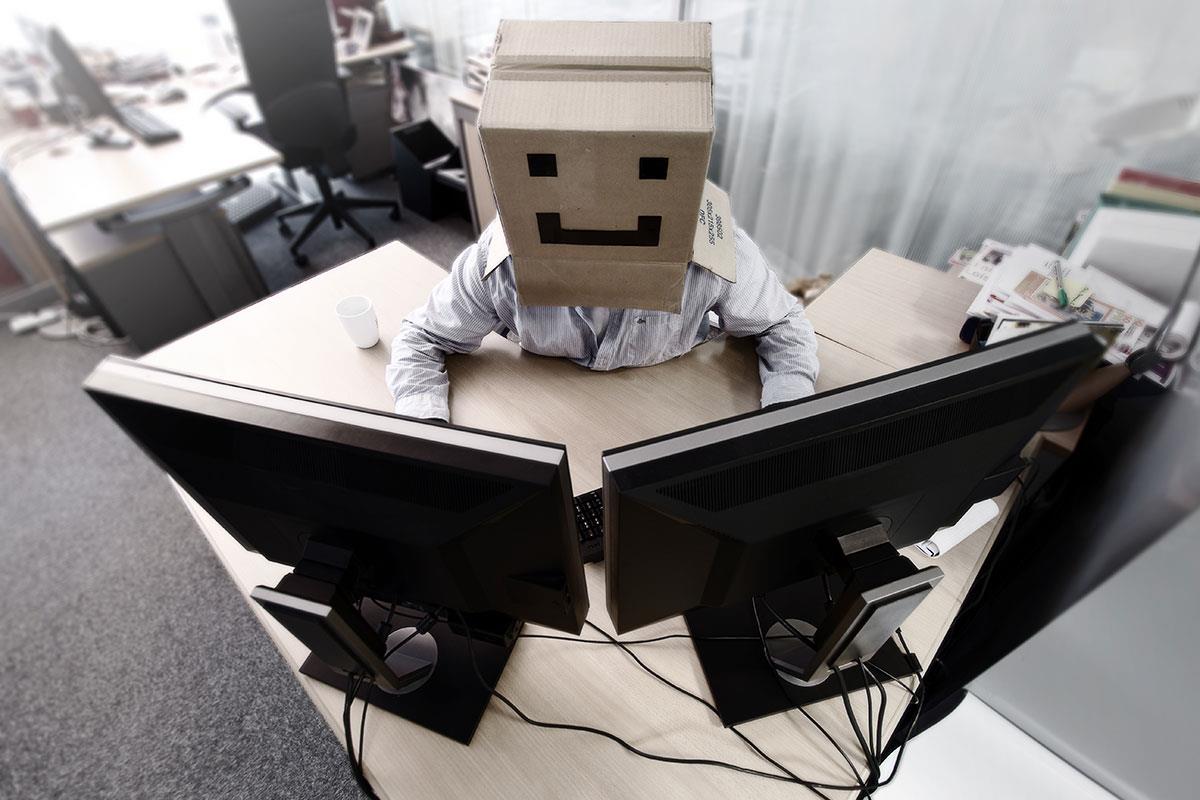
The Rise in Virtual Assistants
The Growth of Digital & Virtual Assistants They are referred to by various names including...
EVE Online Makes A Comeback
EVE Online 1 Million Skill Points GiveawayTable of Contents ▼▼▼▼▼ ➥ EVE's Evolution ➥ 1 Mil...
The Trouble with Let’s Encrypt
Lets Encrypt Free SSL SSL certificates all perform the same task, but they aren't all equal in...
What Is a 403 Error?
What Is a 403 Error?Every response on the Web comes with an HTTP status code. Users don't see most...
Stop! Thief! Online Identity Theft
Stop! Thief! Online Identity TheftHow Your Identity is Being Stolen If you've had your identity...
What Is Two Factor Authentication (2FA)
What Is Two Factor Authentication (2FA), And How Does It Benefit Companies? Identity theft,...
Top 10 Minecraft Discord Servers
Top 10 Minecraft Discord ServersTable of Contents ▼▼▼▼▼ ➥ How We Decide? ➥ How To Connect? ➥ #1...
Eco Web Hosting
Eco Web Hosting Solutions The what, when, why and how of it all.Table of Contents ▼▼▼▼▼ ➥ What Is...
Top 5 RUST PVE Servers
Best 5 RUST PVE ServersSo, you are looking for the best RUST PVE servers? Wise choice. Whether...
Covid 19: Should we be concerned about the safeguards?
There have been concerns over the ways that different governments have been collecting and...
Covid-19 Lockdown: Use Your Time Wisely and Learn New Skills Online
The new coronavirus (otherwise known as COVID-19) is now a global emergency, and it has been...
CEO’s BLOG: How is COVID-19 affecting our business
It has been a really busy year for us at OrangeWebsite as we have been working hard internally to...
7 Ways Your Website May be Screaming “I Am Out of Date!”
7 Signs Your Website is Out of DateThere are two types of website owners. Some understand that a...
Whatever Happened To…?
Whatever Happened To... Whatever Happened to....? Computers, the internet, and cell phones are...
It’s Not Just Facebook. Ways You Are Giving Up Your Privacy
It has been referred to as a "breach" and misuse of private information. It has been the buzz of...
The Eleven Most Important Reasons to Choose a Web Hosting Company
The Eleven Most Important Reasons to Choose a Web Hosting Company The factors surrounding your...
Web Hosting for Dummies: What is a 304 Error
What is a 304 Error What is a 304 Error? - Odds are, you use of one of the “Big Five” website...
Organic Web Hosting
Organic Web Hosting The word "organic" means "from the living". Organically grown foods have...
Web Hosting for Dummies: What is a 503 Error?
WHAT IS A 503 ERROR It is not uncommon for website users to encounter error messages when...
Are Data Centers the Steel Plants of this Generation?
Are Data Centers the Steel Plants of this Generation? There was a time when the United States and...
20 Facts About Google in Their 20th Anniversary Year You May (Or May Not) Know
This year marks the 20th anniversary of search engine giant Google. When Larry Page and Sergey...
Just Who Owns the Internet?
Just Who Owns the Internet? Some connect to it, some surf it, and others are addicted to it. We...
Net Neutrality Heading into 2018
Net Neutrality 2018 As the last six weeks of 2017 unfolded, many Americans were preoccupied with...
How Blogging Can Brand You and Position You
Benefits of Blogging for Business Benefits of Blogging for Business There are generally, three...
How Social Media Has and Continues to Change Our World
How Social Media Has and Continues to Change Our World Social media is such an integral part of...
Freedom of Speech, Hate and the Internet. Just What is Legal in the U.S.?
Freedom of Speech in America Freedom of Speech in America - Just what is legal? Much has been...
Catching Up With Bitcoin Value: Where’s It Been? Where’s It Going?
Catching up with the Bitcoin Value! Catching Up With Bitcoin Value: Where's It Been? Where's It...
The Most Internet Restrictive Countries on the Planet
Top 10 Most Internet Restrictive Countries On the Planet! Those who live in the United States...
The Serious Business of Guarding the Images Used on Your Website
How To Protect Your ImagesFor those of us who have lived through the early, “Wild West” days of...
It’s Easy Going “Green”
Going Green Operating on an environmentally friendly basis is becoming more important for both...
Net Neutrality Violations – Protecting Your Privacy
Current News Related to Net Neutrality The refrain in the United States is about “removing...
5 Reasons To Remain Anonymous In An Infamous Age
REMAIN ANONYMOUS IN AN INFAMOUS AGE REMAIN ANONYMOUS IN AN INFAMOUS AGE - With the advent of...
The Many Benefits Of Offshore Web Hosting
Benefits of Offshore Web Hosting Every website must be hosted. And there are a myriad of ways to...
Choosing a Web Hosting Company
Choosing a Web Hosting Company Choosing a Web Hosting Company - A lot of things in life are...
Bitcoin Update
Bitcoin Update The Latest Bitcoin Update and Why It Matters for Your Privacy Bitcoin Update...
Private Internet Access
Private Internet Access Private Internet Access, is there really such a thing? There are many...
What is a 503 Error? Understanding the Error and How to Fix It
What is a 503 Error? Understanding the Error and How to Fix It It's a nightmare scenario for users...
What’s The Difference Between Whistleblower & Leaker?
Americans who get labeled a "whistleblower" become a hero. Get labeled a "leaker" and you could...
Freedom of Speech Amendment
Freedom of Speech Amendment How Orange Website Policies Promote Your Right to Publish Anything....
The Importance of Using Anonymous Website Services Online
In a world that is becoming more interconnected with more and more powerful governments and...
Hacking Scandals: The Biggest, Baddest, And Scariest
[vc_row][vc_column][vc_column_text css_animation="bottom-to-top"] The Internet is a worldwide...
The Increasing OAuth Phishing Threat
OAuth Phishing Threat People are gradually growing more careful about phishing schemes that...
Web Hosting Talk: Most Common Web Hosting Problems
Web Hosting Talk on the Most Common Web Hosting Problems There are so many web hosting companies...
What Can We Learn from the Cloudflare Leak?
What Can We Learn from the Cloudflare Leak? Cloudflare calls itself the “web performance and...
The Ultimate How-to Guide for Domain Registration
Ultimate Guide on How to register a domain. Your domain name is one of the most important aspects...
Data Centre Risk Index Names Iceland World’s Safest Location
The 2016 Data Centre Risk Index, published by Cushman & Wakefield (C&W), has moved Iceland...
The Icelandic Modern Media Initiative: A Good Crisis and Evolved Democracy
Democracy is evolving, and Iceland is leading the change. As vigorous proponents of radical...
WorldCoin, the Faster Cryptocurrency
Bitcoin was the first cryptocurrency. It's still the best known and most widely used, but it's far...
Boost your search rankings with an SSL
How to Boost Your Search Rankings With An SSL Why You Should Have an SSL Certificate Have you been...
The Inconvenient Truth about 24/7 Hosting Support
Most of web hosting services providers on the market claim to have technical support team...
Mercedes Hybrid Concept car – The Cutting Edge of Energy-saving Technology
Concept cars often resemble an engineer's most incredible daydreams – the end results are...
Online Shopping – 10 Things to Keep in Mind
Online shopping has changed the retail industry by providing customers with 24/7 access to...
UK’s Internet Troll Policy: A threat to Freedom of Speech or a Better Protection for Individuals?
The United Kingdom recently introduced new sentencing measures for Internet trolls found guilty of...
How Safe are your Personal Data in Modern Online Society?
Facebook and Google are two of the biggest names on the internet today. What lots of people don't...
Christmas Is Near – It’s Time to Share
The holiday season is rapidly approaching and we have published new Christmas outlook on our...
Top 10 Causes Of Water Pollution
Top 10 Causes Of Water Pollution Top 10 Causes Of Water Pollution: Poisoning The Very...
Iceland Airwaves – A Music Festival on Volcanoes
When you think of Iceland, images of fiery volcanoes, imposing mountains, craggy peaks and vast...
How Much Can a Whistleblower Get Paid?
Being whistleblower has never been easy and is certainly at high risk situation. If you are...
Understanding the Right for Privacy on the Internet
It seems like every time you check your newsfeed, there's another story about someone's privacy...
Human Body: Source of Energy Like Never Before
We may live in a high-tech world but majority of us still rely on a rapidly diminishing supply of...
Quick Start Guide for Choosing a Web Hosting Provider
There are so many web hosting companies out there offering so many different options, picking the...
A Major Breakthrough on Carbon Cuts Announced by USA and China
China and the United States have made surprising announcement on cutting their greenhouse gas...
Political Donations vs. Free Speech
Freedom of speech or free speech, is a right to express and communicate one’s opinions and ideas,...
5 Unusual Sources of Green Energy
Finding sources of green energy is a growing challenge for most scientists and companies across...
The Risks of Being a Whistleblower
We all like to think that we would do the right thing if we knew about an illegal or harmful act...
Privacy on the Internet: Your Selfie is a Gold Mine for Marketers
We all love selfies. You constantly see the ones your friends take in your newsfeed and you post...
6 Tips to Choose an Effective Domain name
For some, the process of domain registration and choosing a domain name is a real mystery. But...
Understanding Freedom of Speech in Practice
Freedom of speech is one of the most fundamental rights someone can have. That said, there's a lot...
Real-Life Examples of Why Privacy on the Internet is Essential
In discussions about our digital lives, some people question the need for strict privacy around...
Five Essential Souvenirs from Iceland
If you're going to travel to an exotic destination like Iceland, it's a good idea to get a...
Secure Offshore Hosting: A Whistleblower’s Best Friend
Whether it is the pharmaceutical industry in the news for mislabelling a new drug or a fresh...
Three Myths About Why Renewable Energy Won’t Work
You’ve probably heard a lot of corporate droning about the drawbacks of renewable energy. Powerful...
Freedom of Speech: What It Means In a Connected World
Freedom of Speech should be an inalienable right, but social media makes things a little more...
New Website Online Now
As CEO of OrangeWebsite I am very happy to announce that our completely new website is online as...